Businesses can unanimously agree that 2020 has been a rather trying year for security worldwide. We have seen some of the worst breaches in the last one year. People were forced to work from home which increased the risk of open RDP ports, which in turn resulted in numerous data breaches.
Some of the key questions that security leaders have are, how does one ensure security for the remote workforce, while also ensuring productivity? What are the risks and gaps in security capabilities? Where should CISOs focus their time and resources in 2021? While these questions can have multiple answers, Gartner says the real question is what are the security projects that will drive business value and reduce security risk in this ever-changing threat landscape.
Here is a summary of the top 10 Security Projects listed by Gartner to drive Business Value in 2021.
Automating Security Risk Assessment
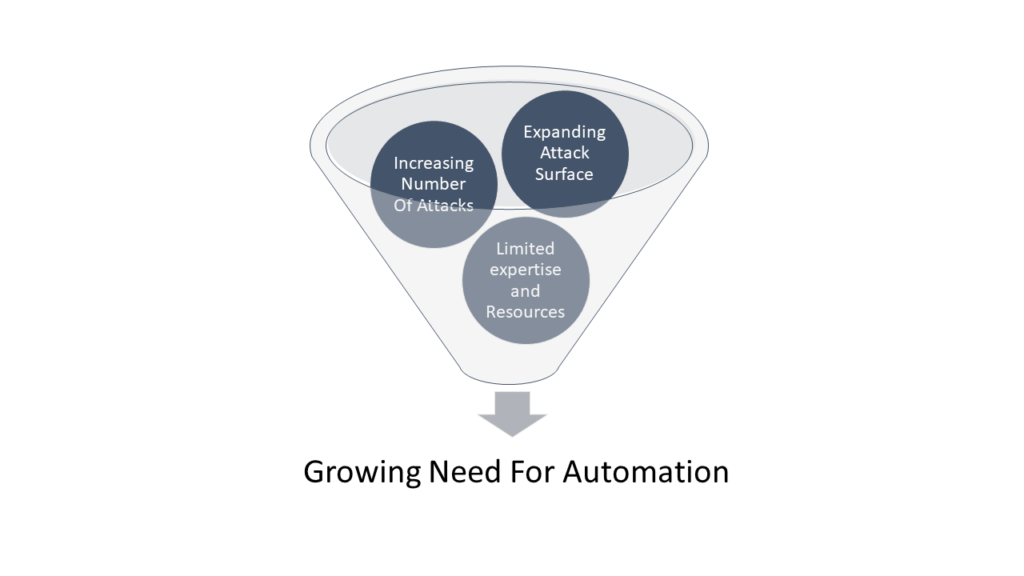
Risk assessment needs to be an automated process so that you as an organization know constantly where you fail. Because attackers are out there attacking all the time. Presently risk assessments are either skipped entirely or done a limited number of times. These assessments will allow for limited risk automation and visibility into where risk gaps exist.
Continuous automated risk assessment solutions are available which can continuously monitor your attack surface and give you a projection of how exposed your assets are.
>>Request Demo For Continuous Automated Red Teaming (CART) & Attack Surface Management
Managing Remote workforce
It’s been over 6 months that businesses were forced to go remote. Now is a good time to reassess and review everything that changed to understand the correct access level and if any security measures like transparency at work, risk-based measures, etc are actually impending work.
Extended Detection And Response
This is a platform that consolidates multiple security into one and may help provide better security outcomes. Organizations use this technique to streamline security.
Risk-Based Vulnerability Management
Focus on exploitable vulnerabilities. Use advanced threat intelligence to understand your attack surface, an attacker activity, and internal asset criticality. This should provide a better view of organizational risk.
Cloud Security Posture Management
Organizations need to ensure common controls across IaaS and PaaS, as well as support automated assessment and remediation.
Simplify Cloud Access Controls
This is done through CASB. It offers flexibility by starting out on monitoring mode to better ensure proper traffic and understanding security access.
DMARC
It’s a domain-based message authentication, reporting, and conformance, an email authentication policy. Although this is not the whole and sole for email security. But it can be one of the security approaches. It does offer an additional layer of trust and verification over the sender’s domain. It helps in domain proofing, if not help solve all email security issues.
Passwordless Authentication
Employees mostly end up using their personal email password for all their work-related stuff too. This causes major security gaps. Passwordless authentication can work in many different ways and offers better security.
Data Classification and Protection
The nature of data varies, so does the mode of security. One security fits all kinds of data is not correct. It either creates too much security or too little. One first needs to get the right definitions and policies but layering security technologies.
Workforce Competency Assessment
Just like in a football match you cannot have a Goalkeeper play center forward, in an organization people with the right skill set need to have the right role. Assess competencies in a range of ways, including cyber-ranging and cyber simulations and softer skill assessments.











