Agentic AI Penetration Testing for Web Apps and APIs
Discover your real attack surface, prove what is exploitable with a working exploit, and chain findings into multi-stage attack paths. Continuously, and under your control.
The annual pentesting world is gone
That world is gone. Teams deploy weekly or daily, and attackers now move at machine speed. Three structural gaps open the moment testing runs on a calendar.
Tested vs attacked
Most programs test crown-jewel apps and leave shadow apps, forgotten subdomains, and API endpoints untouched. Attackers probe 100% of the surface.
Scanner false positives
Scanners flag issues in isolation. Real attackers chain them. 22% of breaches start with credential abuse, and 20% begin through a peripheral asset.
vs a 3-day exploit window
Many teams still test once a year. Attackers exploit new CVEs in about 3 days. The gap widens with every release you ship.
One platform: AI pentesting with AI safety and governance built in
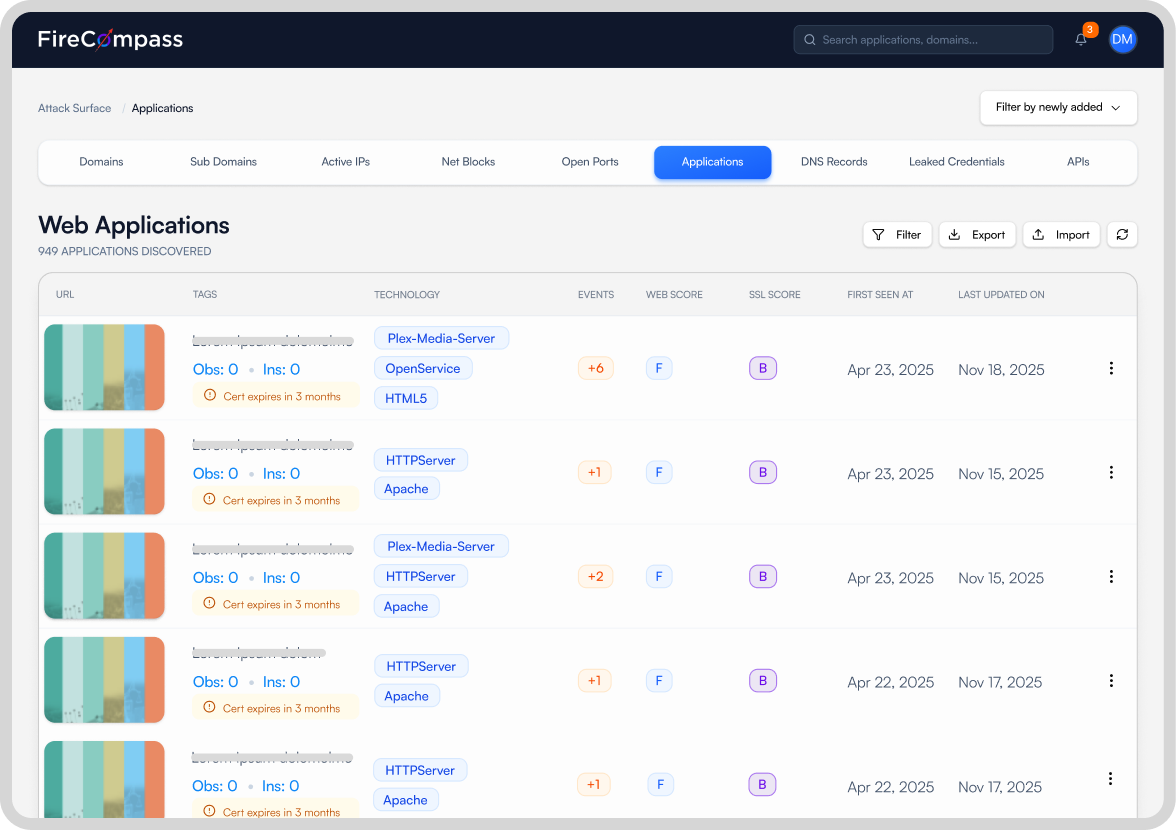
Discover your real attack surface
You cannot test what you cannot see. Agents map the surface an attacker sees, starting from just your org name.
- Shadow apps and forgotten subdomains
- API endpoints pulled from JavaScript files and traffic
- Leaked credentials on the deep and dark web
- Peripheral assets attackers target first
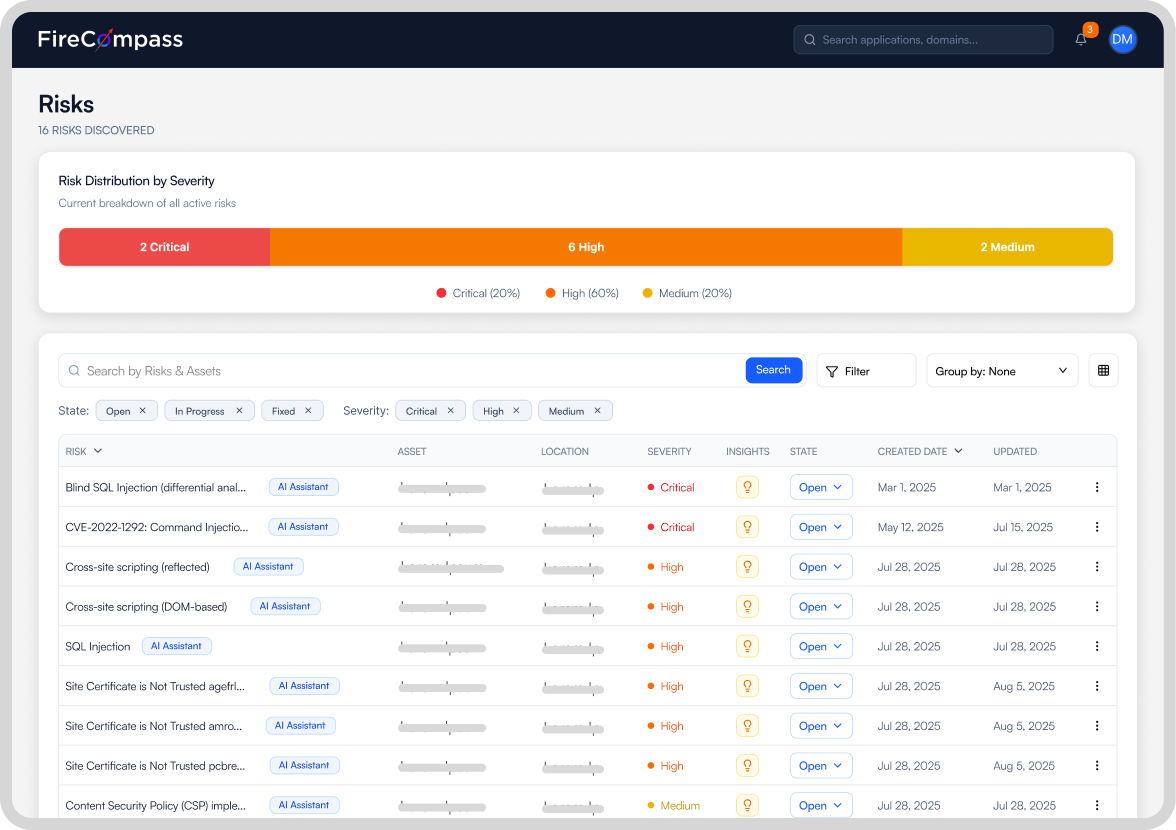
Prove what is exploitable, not just what looks suspicious
A scanner says a vulnerability might exist. FireCompass runs the exploit and attaches the evidence.
- Working exploit and steps to reproduce on every finding
- Ready-to-run proof of concept, for example Python
- Leaked credentials validated to real account takeover, not just flagged
- Under 2% false positives, against 40 to 70% for scanners
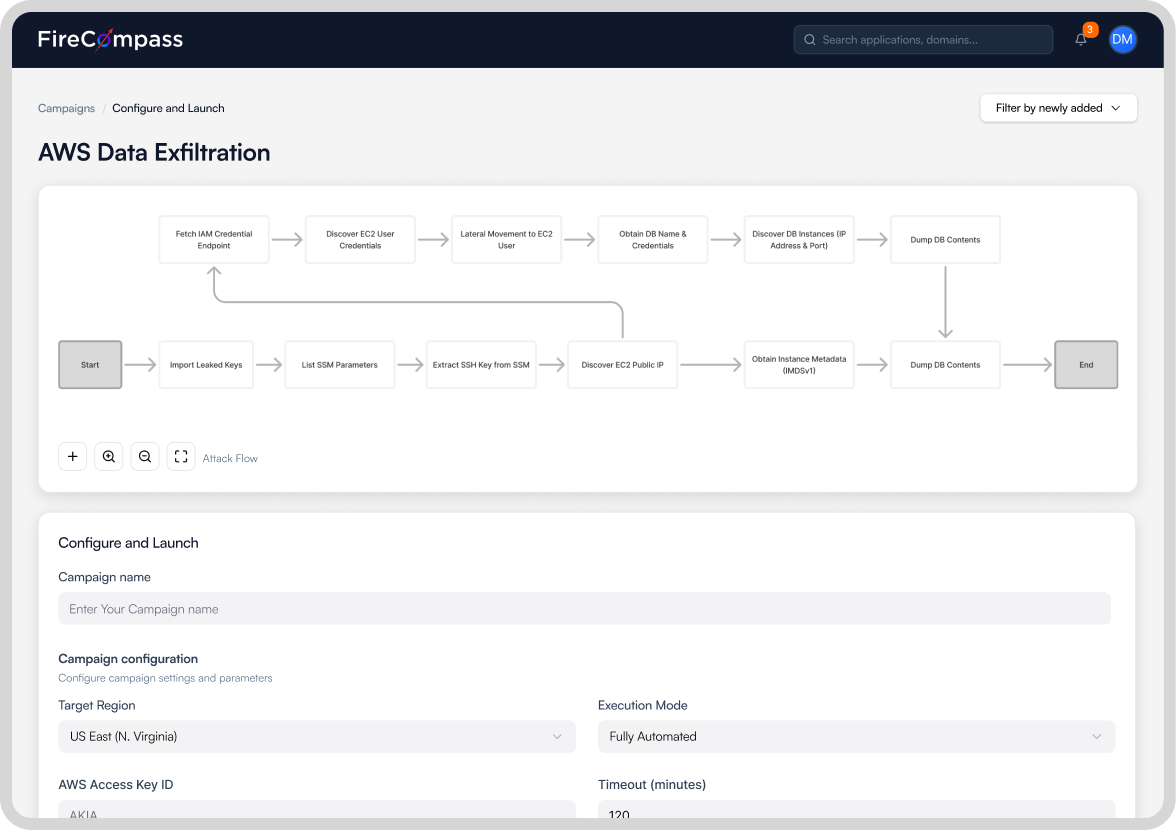
Chain findings into multi-stage attack paths
Findings do not sit in isolation. Agents chain them across apps, APIs, and identity in a single run, the way a real adversary reaches your data, and visualize liveattack paths.
- Credential reuse and account takeover across apps
- App-to-App and App-to-Identity lateral movement, including Active Directory
- Privilege escalation to admin and root
- A live, MITRE ATT&CK aligned attack-path graph you watch during the run
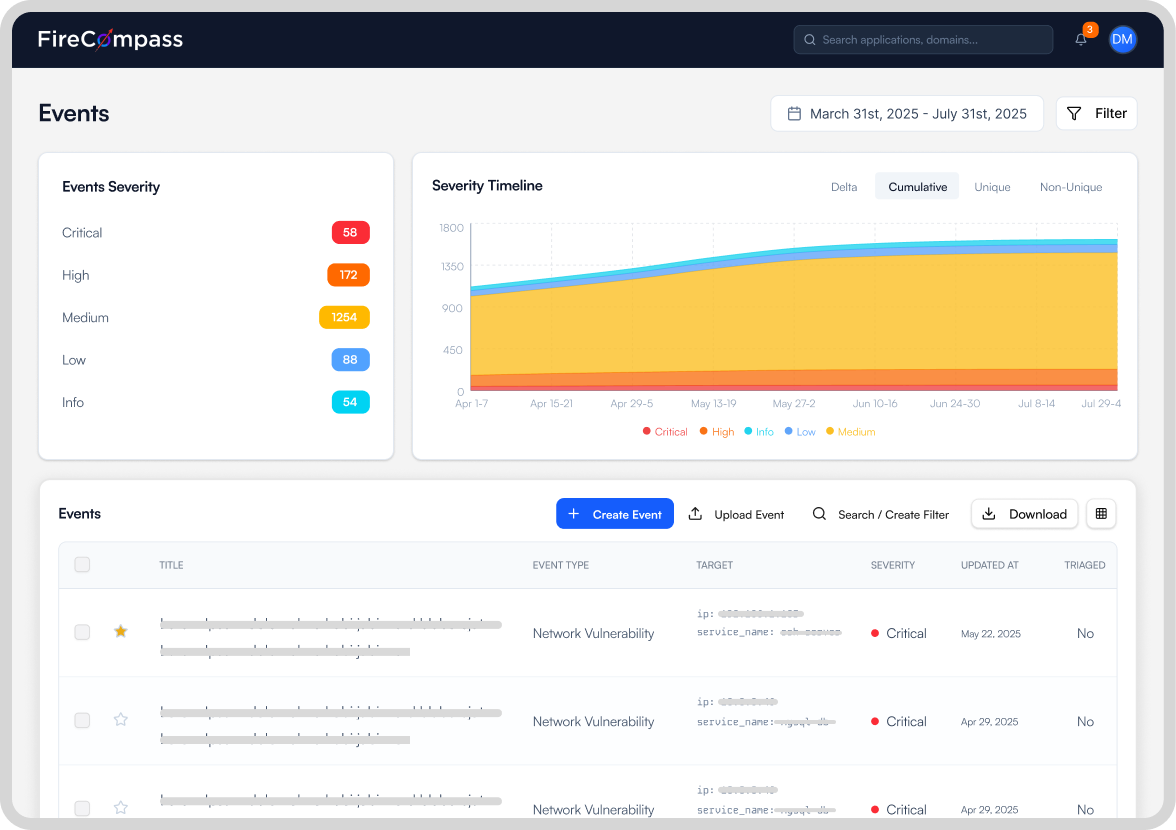
Run continuously, with Enterprise grade AI safety and governance built in
Machine speed testing without handing over the keys. Every agent runs inside guardrails you set, and every action is logged for audit.
- Transparency into every agent plan, decision, and action
- Scope control over what agents can and cannot touch
- Safe exploitation that confirms impact without breaking production or moving real data
- Full audit trail to evidence SOC 2, PCI DSS 4.0, and ISO 27100 testing cadence
Exploit-validated findings, benchmarked in the open
See how FireCompass agents chain findings into multi-stage attack paths
A security expert will walk you through how the agents discover, exploit, and chain findings, with a proof of concept on every issue.
Attackers chain across apps and APIs. So does our AI agent, at machine speed.
Single-shot AI tools fire payloads at one target and stop. FireCompass discovers your surface first, proves what is exploitable, then hops app to app and into identity the way a real intrusion unfolds. The moat is not the model. It is the orchestration, governance, and repeatability around it.
| Capability | Vulnerability scanner | Human PTaaS | ASM only | Single-shot AI | FireCompass |
|---|---|---|---|---|---|
| Discovers your full attack surface first | No | Scoped slice | Yes | No | Yes |
| Pentests with exploit-validated PoC | No | Yes | No | Yes | Every finding |
| Chains across apps, APIs, and identity | No | Manual | No | Single target | Yes, autonomous |
| Leaked credential to account takeover | No | Manual | No | No | Yes, validated |
| Live attack-path visualization | No | No | No | No | Yes |
| Runs continuously, on every change | Yes | Every few weeks | Yes | On demand | On every change |
| Expert-in-the-loop option | No | Humans only | No | No | Optional |
| False positive rate | Up to 70% | Variable | High | Variable | Under 2% |
| Cost per app | $1,400 to $2,900 | $2,400 to $10,000 | Low | Varies | > $1,000 |
Featured in the Gartner Hype Cycle 4 times in a row.
Go deeper
Build a Mythos-ready pen testing program
Why LLMs alone are not enough for enterprise-grade pen testing, and what a continuous, exploit-validated program looks like.
Gartner: "The Future of Pen Testing Is Continuous Offensive Security Testing (COST)"
It unifies discovery, penetration testing, attack-chain validation, and red teaming into one continuously operating capability.
AI web application pentesting whitepaper
How agentic AI delivers 99%+ coverage, under 2% false positives, and real attack-path validation.
Frequently asked questions
What is agentic AI penetration testing?
How is it different from a scanner or DAST?
How is it different from single-shot AI tools?
Is it safe to run on production?
How do you keep the AI agents safe and governed?
How fast is a pen test, and what does it cost?
Does it replace human pentesters?
Hack yourself before AI does
Attackers already test at machine speed. Now you can too. Start with a free pen test and see what they would find first.
