Continuous Attack Surface Management (ASM) And Monitoring
Track Known & Unknown Assets Before They Are Exploited
Continuously Identify, Prioritize and Monitor Risks Coming From Internet Facing Assets & Systems
Research indicates that 30% of organizational breaches occur due to the shadow IT assets or vulnerabilities in the cloud created without the knowledge of the IT security team. Some recent attacks include the like of the SolarWinds attacks in which malware was introduced through its supply chains, the Colonial Pipeline ransomware attack in which remote services such as remote desktop protocol (RDP) was used to gain access, the Capital One attack in which a vulnerable web application and a remote access server exposed on the internet was used to gain unauthorized access.
Failure to conduct an extensive attack surface analysis leaves low-hanging fruits easily exploited by cybercriminals without the knowledge of security experts. That is why it is crucial to conduct an attack surface mapping and an attack surface reduction and management in order to reduce unknown risks
Potential Risks Without Attack Surface Monitoring Tools:
In 2018, Gartner suggested security leaders to start reducing, monitoring, and managing their attack surface as part of their holistic cybersecurity risk program. Attack Surface Management needs to be a top priority for CIO, CISOs & security teams.

Runs Continuously . No Software. No Hardware. No Additional Resources
FireCompass helps to evade external breaches which might happen due to vulnerabilities in risky assets where the organization has no attack surface visibility or has lost visibility
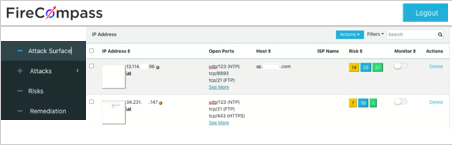
FireCompass helps organizations to reduce their Digital Attack Surface by identifying all unnecessary open ports/services & all possible vulnerabilities from Known and unknown assets
FireCompass continuously analyzes the internet and provides alerts on any changes or risks associated with your digital footprint


FireCompass helps to reduce attack surface by providing Digital Attack Surface Visibility & Mapping to help organizations remove assets which are not in use or not required.
FireCompass tool identifies, analyses and prioritizes digital risks. The dashboard summarizes the high, medium, and low priority risks and recommends mitigation steps.
Continuously Monitors Attack Surface and alerts on any changes, including new ports or internet-facing infrastructure.

Discover strategies to reduce your attack surface.
Find insights on the areas of your attack surface.
FireCompass is a SaaS platform for Continuous Automated Red Teaming (CART) and External Attack Surface Management (EASM) that acts as an integral part of a good exposure management program.
Request Demo
You have successfully joined our subscriber list.
See your organization’s attack surface from a hacker’s viewpoint: Digital Attack Surface & Shadow IT, Exposed Database,Cloud buckets, Risky Ports, Misconfigured Infrastructure, Code Leads & more)
FireCompass – An EC Council Ecosystem Company.
©2025 . All Rights Reserved.