FireCompass Automated Platform For Indexing, Recon & Attack
Single Platform For Automated Recon & Multi Stage Attacks
Firecompass Recon and Attack platform continuously scans the entire internet including customers externally exposed IT Assets without the need of any software or agents to be installed by the Organization. Organizations can access Firecompass’s SaaS portal dashboard to measure, assess and manage their IT attack surface in order to secure them before hackers target them.

FireCompass runs continuously and indexes the deep, dark and surface web using the same elaborate reconnaissance techniques as threat actors.
Firecompass uses elaborate reconnaissance techniques same like the threat actors and the platform automatically discovers an organization’s dynamic digital attack surface
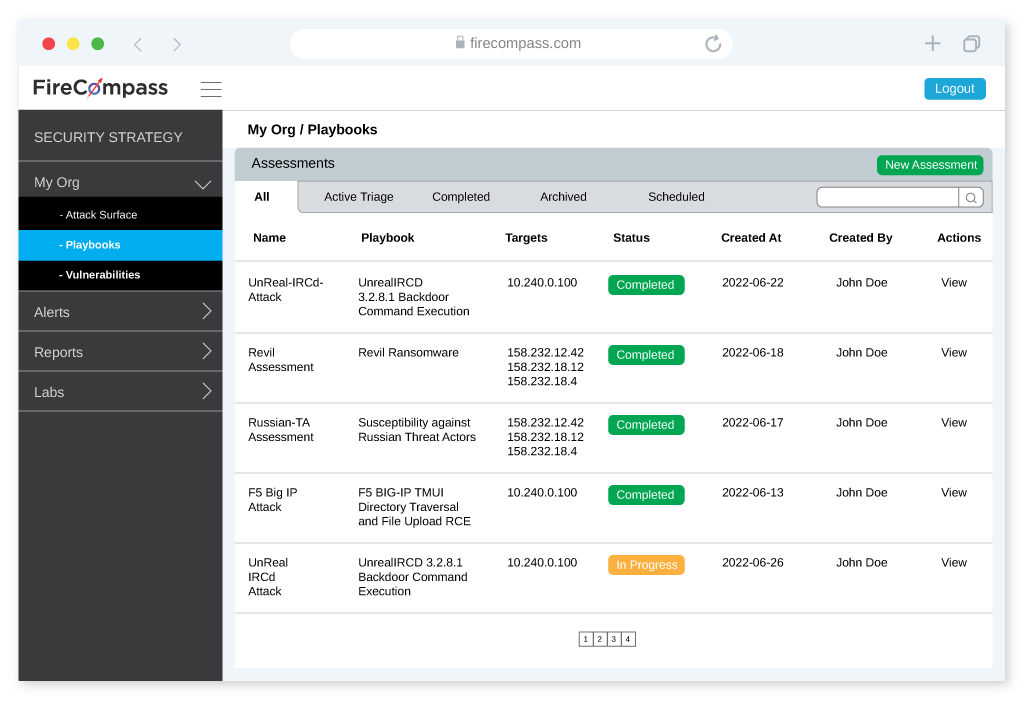
FireCompass continuous red teaming tests your complete attack surface to identify blind spots in your security program. The engine launches multi-stage attacks on your attack surface and identifies the breach and attack paths.
FireCompass runs continuously and indexes the deep, dark and surface web using the same elaborate reconnaissance techniques as threat actors.
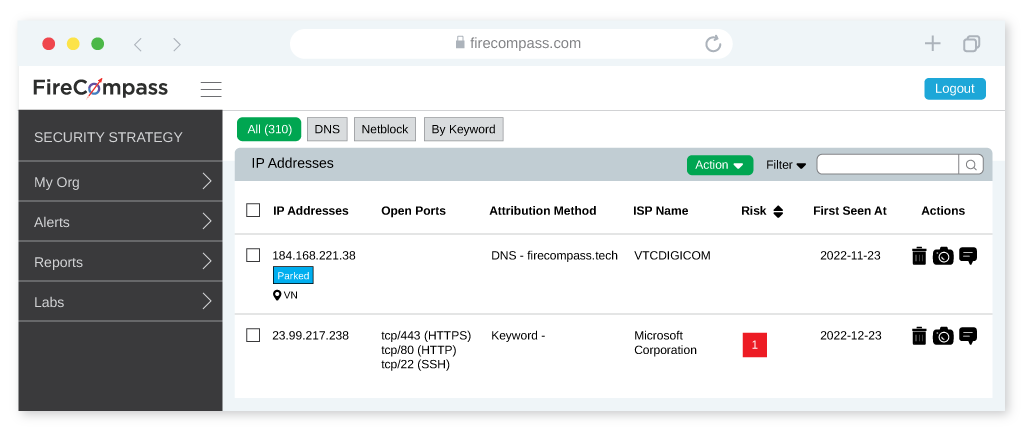

Firecompass uses elaborate reconnaissance techniques same like the threat actors and the platform automatically discovers an organization’s dynamic digital attack surface, including unknown exposed databases, cloud buckets, code leaks, exposed credentials, risky cloud assets, and open ports & more.
FireCompass Continuous Red Teaming tests your complete attack surface to identify weakest links in your security program and helps you to focus on your business critical assets. The engine launches multi-stage attacks, which includes network attacks, application attacks, and social engineering attacks, on the automatically discovered digital surface to identify breach and attack paths. Attack engine is used to:
FireCompass runs continuously and indexes the deep, dark and surface web using the same elaborate reconnaissance techniques as threat actors
FireCompass automatically discovers an organization’s ever changing digital attack surface and the dashboard summarizes the high & low priority risks & recommends mitigation steps.
Authorize the scope of where you want to launch the attacks and launch multi-stage attacks to identify breach and attack paths before hackers exploit

We’ve put together some top talks from global security conferences that could help you get a hang on the debatable topic

Here we list 10 tools which can be used for Reconnaissance by Security teams in order to assess their own security posture against hackers.

We have listed a few breach response tactics that organizations need to keep handy for rainy days. Read to know more about how you can keep your organization safe.
Request Demo
You have successfully joined our subscriber list.
See your organization’s attack surface from a hacker’s viewpoint: Digital Attack Surface & Shadow IT, Exposed Database,Cloud buckets, Risky Ports, Misconfigured Infrastructure, Code Leads & more)
FireCompass – An EC Council Ecosystem Company.
©2025 . All Rights Reserved.