It’s not new news but it’s shocking how large enterprises are becoming victims, these are challenging times. Cognizant (A large fortune 500 company) was seen to notify customers of a compromise and more details. This particular ransomware is particularly dangerous as it steals data before encrypting it and next threatens to release it if the organization isn’t willing to pay. Despite having backups, the company is in a dilemma because their customer’s privacy will be at stake. Interestingly Maze Ransomware workers have made a website to publish the names of the companies who do not cooperate and publish the stolen data
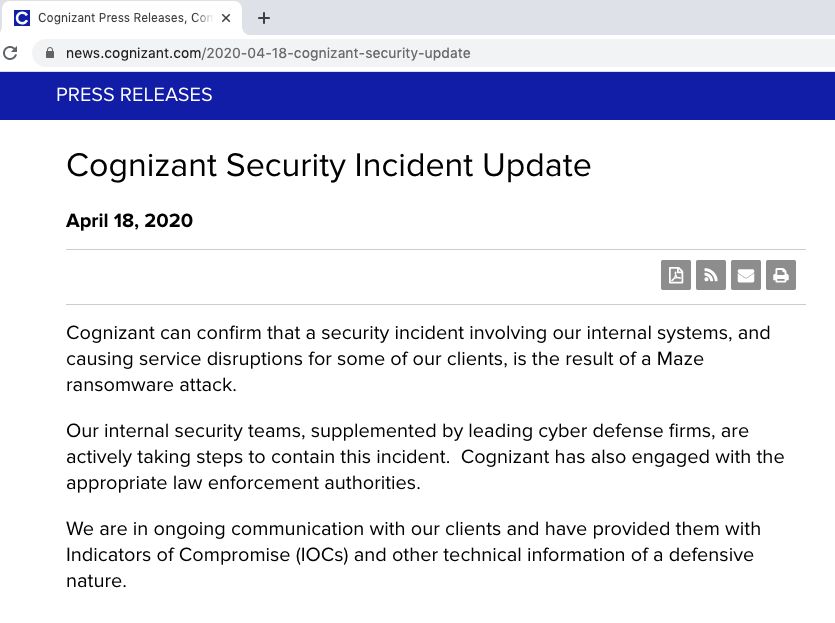
Currently, the company has a statement informing their cyber security team is actively taking steps to contain it. They have had service disruptions in certain areas due to the attack
–>>Check Your Ransomware Vulnerability (Including Maze)
Why It Happened ?
It is know from previous information available, the group uses exploit kits . They have also used phishing emails to trick employees into divulging information by clicking on malicious links. The company hasn’t given details on how their assets got compromised in this case
–>>Check Your Ransomware Vulnerability (Including Maze)
What Can You Learn ?
The above attack is assumed to have used various loopholes at various stages and we can list a few mitigation steps from it.
- Regular Scan For Malicious Activities scanning for red flags, unauthorized access and having the right protocols for automated alerts can be a huge bonus
- Security Awareness Program helps the team members interacting with the company assets taking necessary precaution and help report to the security team incase they notice something suspicious
- Assess Your Attack Surface scan your enterprise assets to understand its current vulnerabilities and exposed assets to prioritize and seal the low hanging fruits first
- Third Party Security measures to make sure any vulnerability doesn’t affect one’s own customers
- PII regulations within the company for careful distribution of PII. Collection of PII only restricted to only when absolutely necessary
- Third Party Risk Assessment Modern tools enable one to understand the threat landscape arising from their vendors
–>>Check Your Ransomware Vulnerability (Including Maze)
References
https://threatpost.com/double-extortion-ransomware-attacks-spike/154818/
https://threatpost.com/maze-ransomware-cognizant/154957/
https://www.techrepublic.com/article/cyberattack-on-it-services-giant-cognizant-impacts-clients/










