The attack surface of an organization can be divided into two parts 1) Digital attack surface and 2) Physical attack surface. An organization should reduce it’s attack surface as much as possible. The more the attack surface, the higher the risks and also the cost to the company to secure them. Here are a few critical steps:
Identify Your Digital Assets Through Manual Approach
Digital attack surface is very complex and typically very large which includes your domains, subdomains, online IPs, exposed APIs, third party libraries, vendor exposures and lot more. It is super difficult if not impossible to identify the entire digital attack surface. You should ask all the key stake-holders to create asset inventory list either in form of CMDB entries or spread sheets. The hard problem is that typically the stake-holders themselves would not have full visibility of their assets. For example a developer may use a third party library or use a third party API without informing or maintaining the list in single comprehensive repository. Marketing team may provide data to a third party email service and may not inform cyber security. Each of these may increase your digital attack surface without the knowledge of the cyber security team.
Automated Discovery of Digital Attack Surface or Shadow IT
- Along with the manual discovery and identification of your digital assets you must also use automated attack surface discovery tools. These tools scan the entire internet to to find if any of the exposed assets belong to you. This can help you to discover the unknown unknowns or Shadow IT created by the organization.
- You may also use CASB products to identify those assets which are used by the organization but may not be owned/maintained by your team for example mobile apps etc.
- Discovering the assets is not enough. For enumerating the attack surface you need to go deeper. As an example for discovering Application Attack Surface you can use the guideline by OWASP: https://cheatsheetseries.owasp.org/cheatsheets/Attack_Surface_Analysis_Cheat_Sheet.html
- There is an interesting research on measuring the attack surface or attackability quotient in this paper: http://www.cs.cmu.edu/~wing/publications/Howard-Wing03.pdf
- For understanding the 3rd party or open source libraries you can use Software composition analysis tools or SCA.
- For monitoring third party or vendors leaking your data you may use Continuous 3rd party monitoring tools.
How FireCompass Reduces Your Attack Surface?
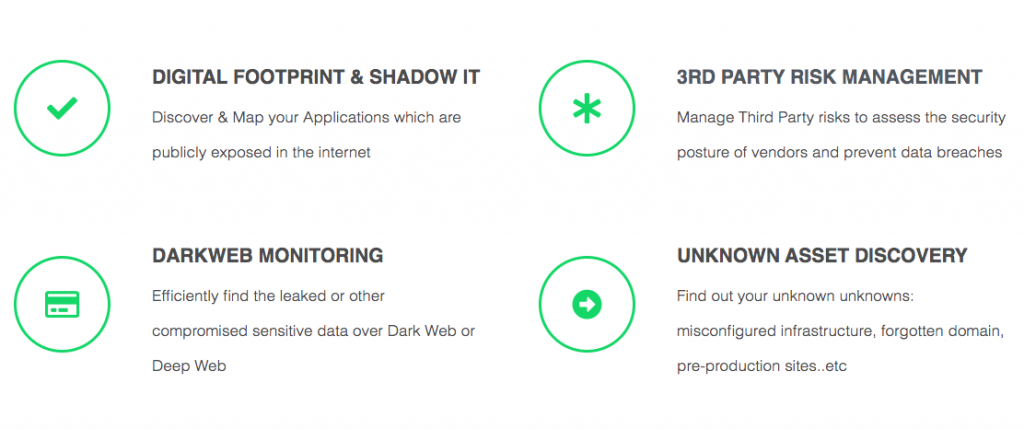
FireCompass helps in attack surface reduction by indexing the entire global internet, including the deep, dark and surface web to discover the unknown attack surface of an organization which is exposed on the internet. It creates an asset inventory of all your publicly exposed applications & services which is stored in FireCompass proprietary Big Data Platform. We query our big-data platform using our proprietary AI and ML based algorithms rendering the results (Shadow IT, Digital Foot print & 3rd Party Vendor Risks) in near real-time.
Bucket the Digital Assets by Business Criticality and Owners
Once you discover the assets you need to find the owners in terms of individuals or departments within your organization. You also need to classify the assets by business criticality. You can create your own buckets. I like the simple High, Medium, Low. You may consider the criticality of data residing in the assets, business continuity impact, brand impact etc while deciding the business criticality.
Determine the Risk for your Digital Assets
You can use a multitude of techniques to determine the risk.
- Digital Risk Protection (DRP) tools. These tools can automatically discover the digital attack surface and find the risks associated with it.
- Use our old friend Vulnerability Assessment and Penetration Testing
- Red Teaming to conduct a real attack.
- Application Security Testing. SAST, DAST, IAST.
- Mobile Application Security Testing
- Application Threat Modeling
- Organization level threat modeling
- Security Architecture review and more..
Prioritize Assets to Bring Down
Once you find the assets and risk, find out which assets you should bring down. It is a joint decision of the asset owners and cyber security. You need to play the role judiciously. You also have to use the knowledge from risk assessment to fix the issues discovered. However in the context of the blog we will focus on reducing the attack surface.
Use Take Down Service for Assets Not Owned by you
There could be some assets which may not be under your control but may pose a big risk for your employees and users. For example lookalike phishing domains. You need to use your DRP partners to use third party take down of such entities.










