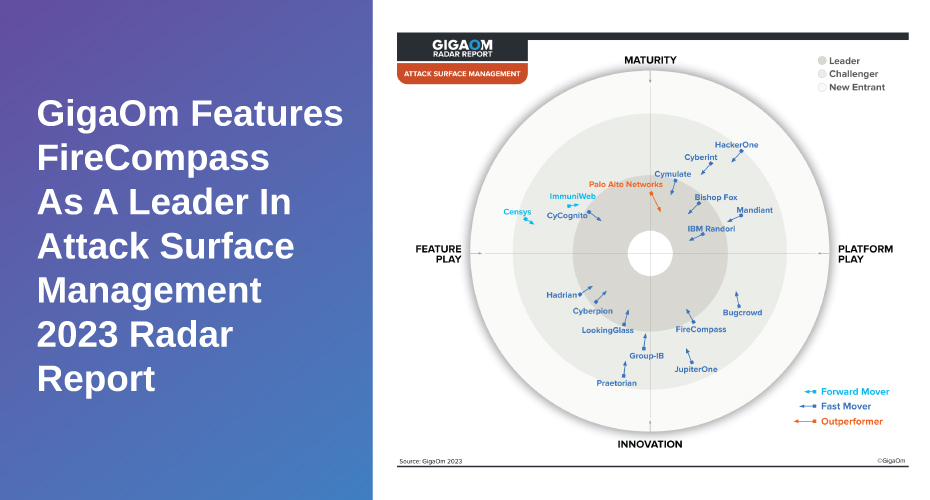
We are excited to be featured as a leader in the GigaOm Radar for Attack Surface Management for our platform’s ability of adversary emulation and automated testing that offers much needed risk verification and prioritization capability to the security leaders. Excellence in critical capabilities like Flexibility & Frequency of Asset Discovery, Active Assessment, Converged Protections, Risk Scoring & Asset Categorization, have put FireCompass in the “Innovation Platform Quadrant”.
FireCompass
“Delivers Actionable Guidance”
FireCompass ASM + CART
GigaOm Radar for Attack Surface Management
>> Get A Hacker’s View Of Your Attack Surface (Request Demo)
The rapid digital growth makes it difficult for organizations to keep track of their constantly evolving attack surface. And this lack of visibility creates more opportunities for attackers to exploit vulnerabilities. Attack Surface Management (ASM) tools help security & risk management leaders continuously discover and gain insights into their organization’s attack surface to better manage and reduce security risks.FireCompass continuously discovers an organization’s attack surface starting with the seed information like domain name. The Platform uses thousands of playbooks to identify and remove false positives during its discovery process.
FireCompass’ Continuous Automated Red Teaming capability is closely integrated with Attack Surface Management (ASM) solution. It enables you to accurately emulate attacker behavior and execute multi-stage attacks. The ASM solution then utilizes the results of these eimulations to further improve the overall ASM process.
The Report specifically points out the risk scoring capabilities of FireCompass Platform. “For example, CVSS scores are the starting point for analysis (as they should be). The proprietary risk scoring algorithm then integrates additional context from various sources, such as the priority of the asset, the weakness of the vulnerability, and the likelihood of exploitation. The end result is a risk score that is easy to digest and actionable”.
FireCompass provides out-of-the-box integrations with other tech stacks, like vulnerability scanners, Amazon Web Services AWS, and Microsoft Azure. To add, FireCompass API is fully documented to meet your additional requirements.
GigaOm Report points out that, “a function that’s not found with other vendors, but solves a common challenge, is how FireCompass integrates with threat intelligence feeds. Threat intelligence is a critical component of an organization’s security program. However, most threat feeds are consumed manually, or it’s left up to vendors to figure out how to use integrations best. FireCompass, in contrast, offers the ability to integrate threat feeds into its playbooks, then the playbooks that impact your assets are selected and run automatically. This approach delivers a timely and accurate assessment of organizational risk found in the attack surface by leveraging up-to-date threat intelligence.”
>> Start Here: Hacker's View Of Your Attack Surface
Most organizations encounter similar issues when they try using traditional vulnerability management processes to tackle the challenges posed by their ever expanding digital footprint, specifically cloud based assets – lack of insights. FireCompass understands the challenge and delivers on its promise from discovery phase through the risk identification phase, leveraging both active and passive assessment methods and moving onto the reporting and alerting phases.According to the report, “The FireCompass ASM solution has a powerful discovery capability matched with passive, active, and multiple-stage risk-validation methodologies. Those, together with a common-sense approach to risk scoring, make FireCompass easy to use as it delivers actionable guidance.”>> Request A Free Assessment of Your Attack Surface Today
About FireCompass:
FireCompass is a SaaS platform for Continuous Automated Red Teaming (CART) and Attack Surface Management (ASM). FireCompass continuously indexes and monitors the deep, dark and surface webs using nation-state grade reconnaissance techniques. The platform automatically discovers an organization’s digital attack surface and launches multi-stage safe attacks, mimicking a real attacker, to help identify breach and attack paths that are otherwise missed out by conventional tools.
Feel free to get in touch with us to get a better view of your attack surface.