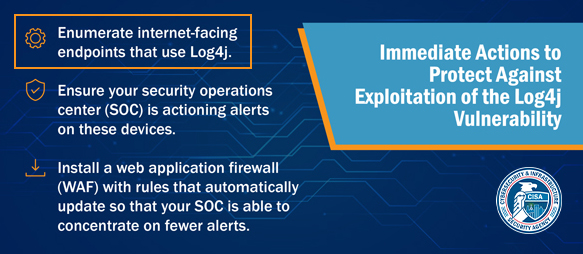
CISA Recommendation: Enumerate Internet-facing Endpoints That Use Log4j
CISA (Cybersecurity and Infrastructure Security Agency – USA) requests every organization to check Internet-facing assets for exposure to Log4j – Start by enumerating “internet-facing endpoints that use Log4j”
Detect Log4J Vulnerabilities using FireCompass Playbook
FireCompass Autonomous Red Teaming Platform has launched a playbook specifically designed to hunt Log4j vulnerability across the internet.
- Unlike conventional tools, discover Log4j issues in both known as well as shadow IT assets
- Perform safe detection of vulnerability by fuzzing various headers and query parameters of the target application
- Specific Playbook to hunt Log4j vulnerability across the internet
"The tool has exceeded our expectations"
- Risk Manager, Sprint USA (now part of T-Mobile)

Single Platform For Continuous Discovery & Testing Of Your External Attack Surface
External Attack Surface Management (EASM)
Identify all IPs, Applications, exposed database/cloud buckets, code leaks, leaked credentials, vulnerabilities, exposed test/pre-production systems, etc.
Continuous Automated Red Teaming (CART)
Launches multi-stage attacks on your attack surface and identifies the breach and attack paths.
Ransomware Attack Surface Testing (RAST)
Discover ransomware attack surface and it’s risk by scanning entire internet for risky assets potentially belonging to the organization



