Find Your Exposed IT Assets
What Google is to most internet users, Shodan (http://www.shodan.io) is to hackers. It is a search engine for hackers to look for open or vulnerable digital assets. Shodan scans the entire internet and stores the open ports along with services running on all accessible ip addresses. It also provides a lot of information about such exposed ip addresses, devices and ports. Such devices can be computers, laptops, webcams, traffic signals, and various IOT devices. This can help security analysts to identify the target and test it for various vulnerabilities, default settings or passwords, available ports, banners, and services etc. Similar to Google dorks, we will present here a few Shodan dorks which can help security analysts uncover digital assets which should ideally not be exposed to the external world.
Disclaimer: This following information is provided for learning purposes, we are not responsible for any misuse, unauthorized or malicious activity done by anyone using such information.
Open Databases
1>Older relational databases like MySQL, PostgreSQL are usually fairly secure by default. They listen on the local interface only and provide some form of authorization by default. However, the same is not true for some of the newer NoSQL databases like MongoDB.
2>A quick search for MongoDB done on shodan shows more than 48000 such servers.
3>To search specifically for open MongoDB instances, use the following search query:
Search term: product:MongoDB -authentication
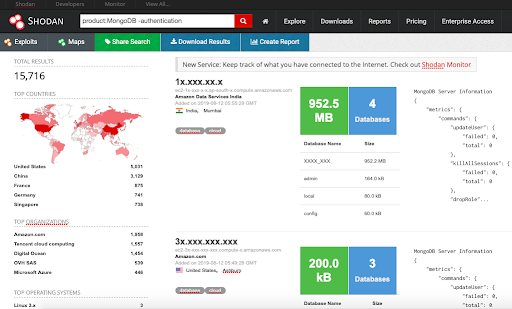
The number of such exposed MongoDB databases is very alarming as it is trivial to copy or delete the data on such databases.
4> To search for Mongo express the web GUI for MongoDB, use the following query:
Search term: “Set-Cookie: mongo-express=” “200 OK”
5> Similar queries can be used to find other databases like CouchDB, RethinkDB, Cassandra and others.
Open ELK Stack
Elasticsearch and kibana also do not come with some sort of authorization by default. Hence we find a lot of such exposed servers with the following query for Elasticsearch:
Search term: product:elastic
And the following query for Kibana:
Search term: kbn-name
Open CI/CD systems
Jenkins is a tool for CI/CD which are used by many development teams. Earlier versions of Jenkins came without default authentication. In such cases, hackers may a lot of information about the SDLC life-cycle of the organisation including source codes, secrets and keys, etc. by going through the Jenkins build logs and other exposed data. To search for such exposed Jenkins instances, use the following query:
Search Term: “X-Jenkins” “Set-Cookie: JSESSIONID” http.title:”Dashboard”
Similarly you may find SonarQube, Docker containers, and so on.
Unprotected Remote Desktop
VNC is protocol to access remote desktops. To search for open VNC servers, use the following query: “authentication disabled” “RFB 003.008”
To search for Windows RDP use the following search query:
“x03x00x00x0bx06xd0x00x00x124x00”
Open Caching systems
Memcached is a distributed memory object caching system. A search for open memcached servers can be done using the following:
Search term: product:Memcached
While we wouldn’t expect to see a lot of data stored in such instances as Memcached is a caching layer, however, they may still hold a lot of sensitive information that is temporarily stored on these instances.
Similar search can be done for Redis, RabbitMQ, etc.
Bonus
If you like the job of hunting for such issues as part of security teams for securing the same, search for: “X-Recruiting:” or reach out to us at [email protected]
For more such Shodan queries, look at https://github.com/jakejarvis/awesome-shodan-queries
Know some more interesting Shodan queries? Get in touch at [email protected]