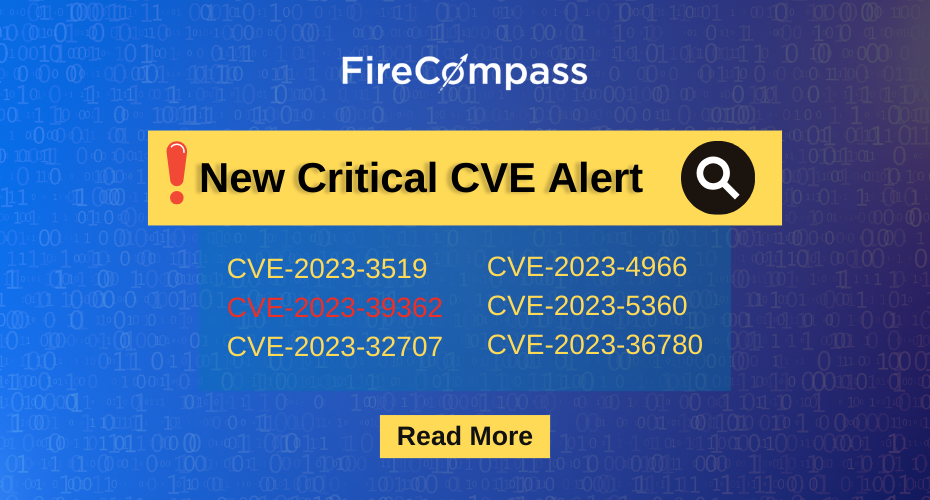
CVE Update October 2023 – New Critical CVE Alert 2023
Welcome to FireCompass Research Team’s Weekly Cybersecurity Threat Report, highlighting critical CVEs and active threats from October 9 to October 13, 2023. Presenting an insightful overview of the latest vulnerabilities, malware, and threat actors impacting the cybersecurity landscape. Stay informed to protect your organization from emerging risks. The Key Vulnerabilities That FireCompass Has Focused On… Read More »CVE Update October 2023 – New Critical CVE Alert 2023